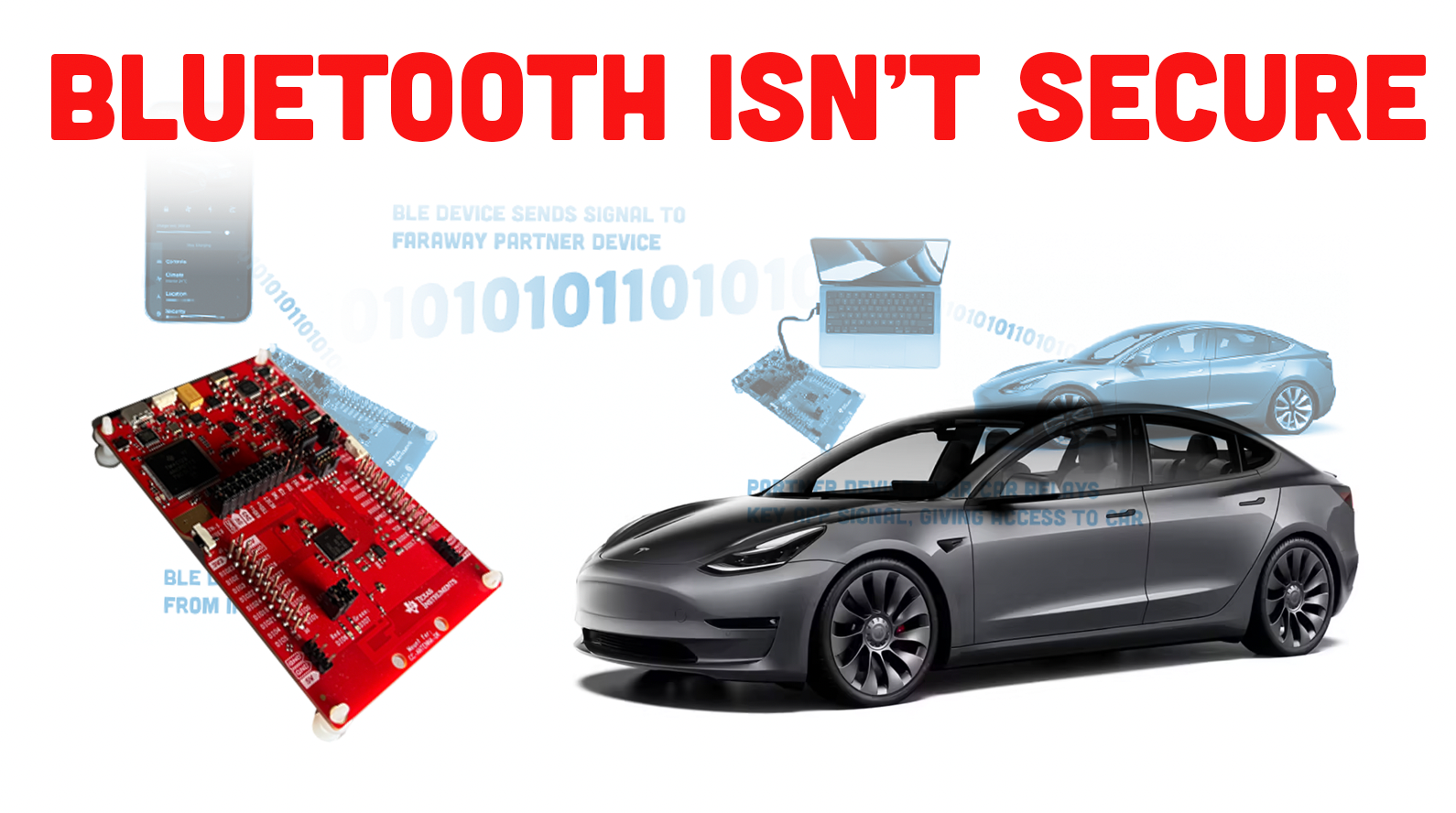
Adapting existing, off-the-shelf technologies from other industries to cars is a clever thing. That’s why color LCD screens are all over the dash of every new car, and why LED taillights are a thing, and on and on. But that doesn’t mean that every technology is actually suited to the unique challenges of automotive use, and now there’s a sobering demonstration of just this idea, as the Bluetooth-based security systems used on Teslas and other cars have been hacked with some clever, cheap devices and methods by a researcher at the security testing organization NCCGroup.
The researcher (and, according to email correspondence from NCCGroup, a fellow Autopian reader, so thanks!) Sultan Qasim Khan (actually, he’s a Principal Security Consultant and Researcher) demonstrated how the hack can work as he unlocks, starts, and drives off a Tesla Model Y using a laptop connected to a relay device, which in turn was in contact with another remote relay device that was in communication with the original Tesla key.
Essentially, what is happening is that he is replicating the signals from the car owner’s phone and relaying them, potentially quite far away, to another device near the car. And he’s getting past security strategies that require require certain response times in the communication between the vehicle and the driver’s phone (this response time is referred to as latency).
Here’s how NCCGroup describes it:
The Tesla Model 3 and Model Y employ a Bluetooth Low Energy (BLE) based passive entry system. This system allows users with an authorized mobile device or key fob within a short range of the vehicle to unlock and operate the vehicle, with no user interaction required on the mobile device or key fob. This system infers proximity of the mobile device or key fob based on signal strength (RSSI) and latency measurements of cryptographic challenge-response operations conducted over BLE.
NCC Group has developed a tool for conducting a new type of BLE relay attack operating at the link layer, for which added latency is within the range of normal GATT response timing variation, and which is capable of relaying encrypted link layer communications. This approach can circumvent the existing relay attack mitigations of latency bounding or link layer encryption, and bypass localization defences commonly used against relay attacks that use signal amplification. As the latency added by this relay attack is within the bounds accepted by the Model 3 (and likely Model Y) passive entry system, it can be used to unlock and drive these vehicles while the authorized mobile device or key fob is out of range.
This will all make a lot more sense if you just watch what happens:
Okay, so what is this video showing, exactly? Khan does a great job of explaining, but let’s re-cap here. There’s a small device that looks to be based on a Texas Instruments single-board computer with various wireless signal technologies embedded, a sort of board that sells for about $50 online, and that device is placed within Bluetooth range of the Tesla’s iPhone-based “key” which just means the tesla owner’s phone that has been configured to act as a key. This can be a surprisingly large distance, which in the testing reported by NCCGroup was about 21 feet.
Next, a similar device, this one attached to a laptop, is in communication with the closer-to-the-phone device via longer-distance communication protocols, like cellular data signals. This end of the attack would then approach the car, and send the Bluetooth low-energy (BLE) signals from the near-phone device–wherever in the world that is–to the device near the car, which can then open and start the car as though the owner’s phone was in the car.
Here’s a very simple diagram:

Here’s more information from NCCGroup on the test they performed:
Testing on a 2020 Tesla Model 3 running software v11.0 (2022.8.2) with an iPhone 13 mini running version 4.6.1-891 of the Tesla app, NCC Group was able to use this newly developed relay attack tool to unlock and operate the vehicle while the iPhone was outside the BLE range of the vehicle. In the test setup, the iPhone was placed on the top floor at the far end of a home, approximately 25 metres away from the vehicle, which was in the garage at ground level. The phone-side relaying device was positioned in a separate room from the iPhone, approximately 7 metres away from the phone. The vehicle-side relaying device was able to unlock the vehicle when within placed within a radius of approximately 3 metres from the vehicle.
It’s worth noting that the above refers to a Model 3 used in the test, and the video shows a Model Y, which makes sense as they both use the same system.
Khan described the method of the attack, and gave some nice, alarming scenarios to haunt your dreams:
“This NCC Group research has proven that attackers can more easily than ever, and very effectively, break into – or outright steal – certain smart cars.
“Using this attack method, I was able to unlock and start the car, then drive away in it. NCC Group has repeatedly and reliably tested and demonstrated this full attack against Tesla Model 3 and Model Y vehicles that it was in rightful possession of as a proof of concept.
“In the same fashion, attackers can also unlock people’s houses to gain access for nefarious reasons; or breach businesses. Perhaps worse, they can enter our personal digital domains via our laptops or phones and sift through our work or invade our communications and innermost thoughts and feelings, and access every photo and video taken of our family, and learn about the places we frequent.
“Systems that millions of people rely on daily to guard their cars, homes, and private data are using Bluetooth proximity authentication mechanisms that can be easily broken with cheap off-the-shelf hardware.
“This research was focused on a class of vulnerability known as a “relay attack”. In a relay attack, messages between the key fob/phone and vehicle (or other device being unlocked) are forwarded to each other by relaying devices. This effectively increases the range over which the vehicle and key fob/phone can communicate. Thus, a phone/key fob and vehicle can be made to believe they are close to one another, when in reality they may be long distances apart – even on opposite sides of the world for digital relays like what I have developed.
“Here’s a basic scenario: A victim is at home. Their phone is in the bedroom, and their car in the driveway, locked. The attacker places one relay device in the garden—close enough for Bluetooth signals to travel—and carries the other relay device close to the car. They can then unlock the car, start and drive it away. Once the device is in place near the fob or phone, the attacker can send commands from anywhere in the world.
“In another scenario, an attacker can go to a restaurant or office full of people, and leave a relay device hidden under a table, in a closet or in a bush beside the building. Vehicles belonging to people inside would be parked in a nearby lot. Thieves can take their pick.”
Now, this sort of relay-type attack has been done before, but Kahn and his team are the first to demonstrate it working with the sort of Bluetooth signals used by phones and key fobs. They explain that a bit here:
Neither normal GATT response latency nor successful communications over an encrypted link layer can be used as indications that a relay attack is not in progress. Consequently, conventional mitigations against prior BLE relay attacks are rendered ineffective against link layer relay attacks.
GATT refers to Generic ATTribute and deals with how two BLE devices communicate with one another. And while I admit I don’t know what a “link layer” is, I do know that this is the method that was key to making this work, and Khan’s team seems to be the first to accomplish such a link layer attack over Bluetooth.
None of this is necessarily Tesla-specific, as other carmakers use similar systems. What this is really demonstrating is that while these Bluetooth-based security systems are convenient, Bluetooth was designed to let your computer and other devices have things like wireless headphones, keyboards, mice, game controllers, and that sort of thing. It was never intended to be a protocol for keeping something like a car secure, and we’re seeing the implications of that here.
The other big issue with this vulnerability is that it can’t be fixed with a software update, as it’s an inherent limitation of the Bluetooth low-energy protocol. NCCGroup did have this recommendation:
Users should be educated about the risks of BLE relay attacks, and encouraged to use the PIN to Drive feature. Consider also providing users with an option to disable passive entry. To reduce opportunities for relay attacks, consider disabling passive entry functionality in the mobile app when the mobile device has been stationary for more than a minute. Also consider also having the mobile application report the mobile device’s last known location during the authentication process with the vehicle, so that the vehicle can detect and reject long distance relay attacks.
For reliable prevention of relay attacks in future vehicles, secure ranging using a time-of-flight based measurement system (such as Ultra Wide Band) must be used.
I suppose the takeaway here is that specific protocols for secure automotive use should be developed for these sorts of phone-as-key systems, since using the same protocol that your old Wii used to talk to the Wiimotes just isn’t very secure, shockingly. If you have a car that uses this sort of Bluetooth-based setup, you may want to go back to a key fob or at least be on the lookout for strange small circuit boards in your home and yard.








Living in the city, kept the doors UNLOCKED unless you want the windows broken.
I didn’t read anything about Tesla’s PIN to Drive. Do the other manufacturers with BLE PaaK have something similar?
https://www.tesla.com/support/car-safety-security-features#pin-to-drive
Would’ve been nice to know which cars have this issue already addressed. Like Tesla hasn’t stopped them from accessing the car, but they have mitigated it. PIN to Drive at least puts another layer before they can drive off with the car if enabled.
I know Ford has something similar with their door keypad, but not sure if they have something similar to start the car.
No clue about Hyundai
Can someone… who is probably “much smarter”, much more “tech savvy” = (which is really code for I can operate a iphone 3x, root a samsung device 5x, FUCK and un-FUCK a recent computer 10x+… (all things I have done) but somehow sees the need for the bullshit world of I.O.T to invade his house like Germany took over Europe)… and A HELL of a LOT MORE BULLSHIT LADEN than I…
Explain to me… why is this allowed to happen? Why Are “we”, “society” as a group (not I mind you), my car is 20+yrs old)… “This system allows users with an authorized mobile device or key fob within a short range of the vehicle to unlock and operate the vehicle, with no user interaction required on the mobile device or key fob”?? What is inherently “wrong” with having a connection of any type to a vehicle?
Id also like to know why Bluetooth… is being allowed as a safety device, to stop the threat of a car being pilched? Sure… its cheap. But why bluetooth?
As far as passwords and or security… we as a people.. involved with TECH, are notoriously horrible, I mean downright MISERABLE with safeguards, protections, safety… involving TECH.
—- Went into my bank once and asked: “Why do you need to ask me 5 different questions with specific answers to log into my account online”. But then ya give me a 4dig passcode (that should just be illegal). Most sites.. heck even the weirdest Govt Sites require the most insane combination of letters, numbers capitals and symbols… just to gain an account (for something as “regular as the DMV”). My… wife / other half bitched about changing passwords on various items.
But this is a world where… people stand in a public domain, on their devices using a public signal, to access — any hose of websites…. without a care in the world.
So now that you’ve stolen a Tesla, what will you do? Can you use this to make a duplicate key? Can’t Tesla shut down the vehicle and locate it once reported stolen?
As for conventional keyed locks on automobiles – it is NOT a high skilled attack to pick and decode an automobile lock. Witness any number of the Lock Picking Lawyer videos. So the low tech solution is not necessarily better, as I would gather far more people can figure out how to pick a lock than to master and exploit Bluetooth technology.
Or, I don’t know, just sell cars with regular F’ing keys?
I can’t imagine how people think the marginal utility of the bells and whistles that are enabled by bluetooth wireless keys are worth the risk of these sorts of vulnerabilities.
Same goes for electric parking brakes. See the articles about the Hyundai Ioniq 5 (and others) that have a recall for THE CAR ROLLING AWAY due to a ‘voltage fluctuation’. Just give me an e-brake handle or pedal – which, by the way, I as the customer would greatly prefer anyway.
Yes please. I’m of the mood that any piece of “automatic” or powered equipment in the car that is not absolutely necessary (including power locks, windows, transmissions) ought to be possible to option out. Guess I’m the 1%er on this.
A good article that gets the vulnerability discoverer/author involved in the comments.
That’s a wow!
I’ll still keep visiting https://www.schneier.com/ for my weekly squid fix, but this site is great and really a reflection of Autopia.
Won’t have that problem in my 62 Lincoln…even if you do drive off with it… it’ll break down shortly afterwards lmao
While a concern, it’s fairly similar to hacks that can clone or boost an RFID signal from a fob used for keyless entry and ignition. In either case, you need to match up the signal to the car.
Of course, like the RFID boosts, it does make it pretty easy to nab a car parked in front of your home, since it’s pretty likely the owner’s phone is inside. Given the precautions listed, such as having the app report phone location, this seems perhaps easier to stop than the RFID boosts.
In a very similar way to how car thieves will fail in an attempt at stealing a manual because they can’t drive stick (see many, many stories of such things happening) won’t it be ironic if the most secure cars end up being ones with a regular key and nothing else?
My cars are old. My cars have metal keys. My cars have stick-shifty bits. My cars are unlikely to be stolen.
I like my cars.
Well, at least I don’t have a cell phone. Or, as far as that goes, a car made within the last forty-ish years.
As long as both of these statements remain true, I figure I’m twice as safe from this attack as I would be with just either one by itself.
You do, however, own at least one car that can be picked up by a medium-sized man, which is its own security challenge.
True, but it was manufactured entirely without door locks. You can’t defeat what isn’t there.
I have a cheap car nobody wants so… i win too?
I am just a ROF (Retired Old Fart), but it appears me that this is just another case of a high-tech company using its customers as beta testers. Isn’t this something that should have been caught in testing before the product was released?
Not necessarily, while there is some element of concern there is a whole new explosion we call the Internet of Things. Like the fridges with displays and your door bell having a camera. All of these work on similar technology and anyone dedicated enough can and will break in. When it comes to technology there is always a way in, we have yet to make a perfect lock when it comes to connecting to the internet. Most people just accept the risk (knowingly or not) for the convenience of asking Alexa/Google/Siri what noise whales make when banging when the thought crosses their mind.
SO tell me.. OH great one, what NOISE do whales make when banging?
Hey Jason, I’ve been a fan of you and Dave for years 🙂
The “link layer” of Bluetooth is what handles things like connection establishment and maintenance, channel hopping, transmit/receive timing, and some other things like that. It’s not something normally visible to end users or mobile app developers – it’s abstracted away by Bluetooth controller chips and Bluetooth stacks. What Bluetooth stacks expose to application developers is GATT. GATT provides a structured mechanism for devices to exchange data, but it provides no visibility or control of how the underlying radio hardware sends the data.
It’s possible to establish two BLE connections with standard Bluetooth controller hardware (the kind you’d find in your phone or laptop), and conduct a relay attack by forwarding GATT requests and responses coming out of your operating system’s Bluetooth stack using standard APIs. This has been done in the past (eg. with GATTacker by Slawomir Jasek), though it had limitations in that it introduced easily detectable levels of latency, and didn’t work with encrypted BLE connections (when the encryption key is unknown).
I built custom radio firmware to handle all the BLE frequency hopping and bidirectional communications, while providing functionality for the connected computer (host) to send and receive raw link layer data. This way, I was able to avoid the conventional Bluetooth controller firmware and the operating system’s Bluetooth stack, while also gaining control of low level radio timing parameters that are normally invisible to higher level software. This allowed me to minimize added latency, and also let me pass along encrypted link layer messages without needing to decrypt them. By doing this, I could conduct relay attacks against targets that couldn’t be relayed with previous tools.
I wouldn’t make blanket statements that Bluetooth is insecure, but rather it is a protocol that was designed for exchanging data, and not proving that two devices are close to one another.
Hello Sultan! First, fantastic name. Also, very glad to have you on here; would you be up for maybe writing something more in-depth for our readers about automotive electronic security? You seem like the man to go to for this!
Sure, I’d be happy to contribute an article or do a Q&A session with you about topics in automotive security that you and your readers would be interested in. You could reach out to me by email, and we could brainstorm topics. If any of the commenters here have any specific aspects of automotive security they’re interested in reading about, feel free to say so too.
Hi, Sultan, great video! One thing I’d be interested in, as a follow up to this, is a layman’s explanation of how UWB would make relay attacks harder? From the article, it sounds like UWB has much lower tolerance for latency, but as data rates for wireless tech increase, it seems like relays could overcome this, if not now, in the near future.
Sure, I could write an article about secure ranging concepts, and how it’s possible to solve relay attacks using a combination of cryptography and the laws of physics.
Technologies like UWB provide time-of-flight measurement. Think of it as sending a ping over the air, and timing how long it takes to get a response. While there would be some delay at the other end between receiving the ping and sending a response, that delay can be made consistent. You can subtract that consistent delay from the time it takes to get a response to your ping, and what you’re left with is the time it took for the signal to reach the other device and back, at the speed of light. You need specialized hardware (like what UWB radio chips provide) to get such precise timing measurements.
You combine time-of-flight measurement with some cryptography to build a system that is theoretically impossible to perform a range extension attack against. In practice, there are some other attacks possible against implementations of this that allow at least limited range extension (eg. Early Detect/Late Commit attacks) but nevertheless it makes relay attacks much more difficult overall, and long distance relays impossible.
Well explained Sultan. You do some cool stuff at work by the looks of it, wish I was on that level on penetration testing but I am not clever or skilled enough for it. Would love to read more stuff from you as Jason suggested and unlike the mechanical deep dives I might pick up more than half of it. Think sec+ would let me write it in as continuing education?
Stared* for that last sentence 😀
*On this site should i say thumbs up? Thumbed up? That sounds a bit personal
Not to take away from the large amount of work that went into this, but I’d love to know why this hasn’t happened sooner. It’s by no means easy, but it also seems like a relatively straightforward approach to the problem.
Similarly, what mitigations would help avoid this? Some sort of frequency-hopping with parameters negotiated in the encrypted channel?
This is obviously a major vulnerability and yet another example of automakers being just inexcusably atrocious at security. However, I feel like any given Tesla-owner (or other person with a similarly-vulnerable car) is probably at very, very low risk of having this happen to them. Perhaps time will prove me wrong, but I’m not exactly going to go tell my mom (who has a Model Y) that this is something she needs to panic over.
“automakers being just inexcusably atrocious at security”
It’s a bit better than the late 90’s and early 00’s when most Ford work vans were keyed so similarly anyone with a key could jiggle it a bit to enter and drive any other Ford van. I’m thinking Chevy’s weren’t much better.
True story: my family owned a 93 Econoline based RV and a 95 ranger in the early 00s when my now wife and I started dating. The Econoline key would start the ranger but not unlock the doors. I “accidentally” took the Econoline keys one evening and locked the truck to get an extra hour or so with my gf before my old man showed up with the proper keys. I know it works on my current obs truck too.
But do tell her to use the PIN to Drive feature for added security.
In reality, these attacks amount to the same cat and mouse games that have been going on for decades. People will say physical keys are the only way to go, but we’ve known about physical key vulnerabilities for a LONG time. I.e. that they can be copied pretty easily. Then came keys with RF, which can also be copied and so on. These wireless vulnerabilities are a little scary because you don’t even need to be in contact with the thief, but it’s still the same song and dance. That being said, this seems like a pretty low barrier to preventing theft with off the shelf hardware and some software (assuming the software can be found with relative ease)
Another great article! Thank you for the good information about the vulnerability of vehicles using Bluetooth. So to be clear…the best way to protect a Tesla (for instance) would be to add a PIN number? Looking to purchase a newer vehicle in the near future and want to ensure that it (most likely) won’t be stolen. I am thrilled that you and David have created this website, I have been a fan of you two for awhile and this website is fantastic.
If I needed to get a “new to me car”… I would rather face the Guillotine and have my head removed or BURNED AT THE STAKE… than buy anything newer than 2005.
Otherwise… if you buy a newer car made in the past 5yrs, you D E S E R V E to have the fucking thing stolen. It spies on you: 5g / GPS sourced service, its written into the contract from the OEM that they will be using info gathered from your OBD-II in your general travels with THEIR vehicle…
The vehicle does everything for you… including make the E N T I R E A C T of driving itself… so god damn boring… that there is no physical contact to the vehicle or its drive ELEMENTS. On top of.. your desire to stare the screen.. instead of driving… is purely ON PURPOSE.
AND… the BEST way to protect a LAPTOP on 4 wheels… is a 4dig pin?!
What ya do is this:
Ya wire in a fuel cut off switch
Ya put in a IGNITION SWITCH, then wire in a ignition cutoff switch
Ya wire in a POWER cut off switch.
— With Toggle Switches.
Then ya get a big ol damn METAL key, use 1 for each door.. plus one for the trunk.
AND.. ya yank out that shitball motor and trans its got.. and shove in a 6spd manuel with NO SYNCROS! NOW, watch the FUCK NUTS try and steal a fucking car again…
This is either the greatest tongue in cheek comment in history, or someone needs their medication dosages adjusted. Upwards. Significantly.
Im going to go with “Greatest Tongue in Cheek comment in history”.
This guy clearly hasn’t watched Lockpicking lawyer if he thinks a metal key is going to be any better.
Has he ever picked an automotive lock? I’m sure he could do it, I’ve just never seen a video of him doing it.
Car locks do have a lot of pins, but probably only moderately tight tolerances. I’m sure he could do it, but it might take a whole minute. Maybe even several, the first round.
I should add, most modern cars have a chip in them that’s needed for ignition. Just the physical pick would get you in the door, though.
Mine isnt most.
Question you have to ask yourself… is this.
I drive a 05 Honda Element…. who is going to steal it?
Thing is, I don’t think Bluetooth was ever designed to be secure. It was designed to be a wireless replacement for short distance connectivity, like headphones, speakers, keyboards, and mice. It just uses discrete digital channels to prevent interference, so your mouse doesn’t end up typing stuff on your screen.
It shouldn’t be used for secure applications, and when car companies and others tell you it’s secure they’re fooling themselves, and you.
Great article, Jason. Thanks for keeping us up-to-date on this sort of thing. It’s appalling how little industries think about security when it comes to stuff like this. I just bought my first all electric car and I chose a 2017 Fiat 500e mainly because it doesn’t have all the “self-driving” bullshit, nor does it have bluetooth based “keys”, etc. It’s basically a normal 2017 Fiat 500 that has been converted (by Fiat) into an electric vehicle. Sure it only has ~100 miles range, but that’s honestly been plenty for trips around town or into nearby (20 miles) Denver and back. I was an electric car skeptic before, but a buddy who owns a Tesla convinced me that it’s not as terrible as people make it out to be. On the contrary, I’ve already sold my beloved Volvo C30 and I’m already planning to replace my Tundra with an F-150 Lightning, but I will NOT be using the “phone as a key” option at all.